Posts
 By Kenneth D. Thompson, WBA Board chair, president and CEO of Capitol Bank, Madison
By Kenneth D. Thompson, WBA Board chair, president and CEO of Capitol Bank, Madison
After the challenges of the last several years, I believe I speak for everyone when I say I am continually amazed by the optimism that Wisconsin bankers hold not only for the growth of our industry, but for our economy and communities as well. Although the COVID-19 pandemic continues to wreak havoc, I expect 2022 to be a year of immense growth and transition within our industry.
As bankers, we are fortunate to have a unique perspective on our economy and communities. As many member CEOs highlighted in WBA’s recent Economic Conditions survey, despite recent obstacles, a majority of Wisconsin bankers rate the current health of the economy as ‘good’ and predict this to stay the same well into 2022.
Our work in providing flexibility to our staff and customers, as well as exceeding expectations of managing liquidity and technological growth in 2021, has absolutely aided in our efforts to provide stability in times of uncertainty. Our industry will continue to be challenged into 2022 as we face inflation; ongoing COVID protocols surrounding vaccinations, boosters, and possible mandates; as well as talent retention.
However, as mentioned repeatedly by Minneapolis Federal Reserve Bank President and CEO Neel Kashkari during WBA’s annual Midwest Economic Forecast Forum, Wisconsin’s economy and our region as a whole has been on par with the recovery of the nation. Efforts by our community banks have not gone unnoticed and have played, and will continue to play, a substantial role in rebounding our economy.
Of course, innovation will remain the name of the game as banks navigate uncertainty. The next eleven months will certainly show the flexibility, creativity, and expertise of banks in Wisconsin and set our industry apart.
Thank You, Ken Shaurette, for 13 Years at FIPCO!
 By Hannah Flanders
By Hannah Flanders
On December 31, 2021 Ken Shaurette retired from FIPCO’s Information Security and Audit Services after 13 years with the company. Shaurette launched his IT career in 1976 after completing his associates degree in data processing. Over the past two decades, he has also garnered a collection of training courses through venders and trade schools as well as certifications by the National Security Agency (NSA) in Information Assessment Methodology. In 2008, Shaurette was hired at FIPCO to build the Information Security and Audit Service from the ground up as its director.
Shaurette shared reflections on how the industry has changed over his decades of experience. When his career began, data was stored centrally in large computer data centers. Slowly, the industry began to give more processing power and ability to manipulate data to users and as the data became increasingly decentralized, security professionals had to establish improved policies and information security programs that addressed data no longer being stored in a big computer center, but out at the desktops anywhere in the company.
As data collection and storage abilities improved, not only did it become more difficult for all the information to be properly secured, it became increasingly important. Regulations have been created today in order to meet the expectation that customer data is equally protected no matter the size of the bank. “Information security [must continue to be] part of our individual and our companies DNA” says Shaurette. “Without security controls, your business can’t grow quickly.”
Shaurette’s perspective has allowed him to help banks throughout Wisconsin protect themselves against serious attacks that could in turn affect growth, reliability, and profits. Shaurette notes that “when it comes to information security 80% is the same regardless of [the] industry when securing the data, 15% is unique to the [banking] industry, and probably 5% is the social atmosphere of [each bank].”
“Over the course of the years, his expertise and service have been greatly appreciated and well-respected by our customers and members,” says Pam Kelly, president of FIPCO. “His passion and unfailing dedication to information security and our members has helped hundreds of bankers keep critical data secure, avoid attackers, and meet the needs of their own communities. Thank you, Ken, for 13 years!”
In his retirement, Shaurette looks forward to spending time with his grandchildren, volunteering, and — he jokes — not writing audit reports. However, he leaves FIPCO customers with one last message in appreciation over that last 13 years, “I may be boating off into the sunset, but the sunrise of a new generation is transitioning behind me, and you will be left in very good hands with Rob Foxx. I’ll be waiting for you to show up for an information security peer group meeting or networking round table on the pontoon boat someday soon. Those that know me, the refreshments are always ready.”
 By Kenneth D. Thompson, WBA Board chair, president and CEO of Capitol Bank, Madison
By Kenneth D. Thompson, WBA Board chair, president and CEO of Capitol Bank, Madison
January marks the halfway point of my time as WBA chair and as we transition into a new year, there are undoubtedly new things to look forward to as an industry and as an association.
Our successes in 2021, many of which related to the ongoing uncertainty of the COVID-19 pandemic, taught us all valuable lessons I hope can be brought with us into the new year. From low levels of past-due loans throughout our industry to excess liquidity, it’s safe to say that stepping outside of our routine has resulted in spectacular results.
Looking onward to 2022, I encourage bankers to approach challenges with the same curiosity we have for the past two years. As our industry continues to grow, how will each of us lead the way in making Wisconsin banks efficient, diverse, and robust?
WBA has long known that banks are cornerstones in our communities and as such, should be leaders in embracing societal developments. Technology, for both our customers and employees, has been and should continue to be an aspect that sets our industry apart. In embracing these digital channels, banks have a unique ability to meet the expectations of customers while also supporting them with cybersecurity and best technological practices.
Our ability to advance diversity, equity, and inclusion (DEI) efforts, as well as offer flexibility to employees, has the potential to set our industry apart. This is especially important to consider as we navigate through a competitive hiring and retention landscape.
As we all envision a brighter 2022, it serves us to remember that innovative solutions, such as PPP and advances in online banking, have provided our communities with much-needed assistance in the past. We must not be held back by what we are familiar with. This pandemic has taught us all that some of the most effective answers may not be the ones that have been tried before.
It is essential for banks to approach these situations with caution instead of resistance and as always, WBA remains a valuable resource in education, advocacy, and community involvement for each of us as we look forward to what’s to come in 2022.
 By Tom Still, WTC President
By Tom Still, WTC President
The list of economic uncertainties for 2022 is long and complex, with COVID-19 variants, supply chain woes, energy disruptions, climate-change anxieties, and political frictions around the world producing jittery markets.
It’s time to look for trends in technology to calm frazzled nerves on Wall Street as well as Wisconsin’s Main Streets.
Analysts at International Data Corp., the global market intelligence firm, predict the technology industry is on track to exceed $5.3 trillion in 2022 — thus returning to the 5% to 6% annual growth rate typical before the pandemic. The United States is the world’s largest tech market, representing about a third of the projected total at $1.8 trillion.
Tech overcame the 2020 speed bump precisely because COVID-19 triggered so much change. The workplaces of today are no longer easily defined. Changes in business travel forced innovation. Cybersecurity threats led to more investment across industry lines, from financial services to “Mom and Pop” retailers. Phrases such as “quantum computing,” “virtual reality,” and “artificial intelligence” were once the exclusive lingo of computer scientists; today, they’re part of the business plans for many companies.
It all points to bigger tech budgets, greater investment and more innovation pushing through the economic super-structure.
Technology will continue to disrupt many verticals. Health care is being transformed through telemedicine and wearables, not to mention breakthroughs in diagnostics and therapeutics. The jury is out on how effective remote learning has been for students of all ages, but online education will continue to have a role in the classroom. Sales through eCommerce in the United States continue to soar (hence, some of today’s supply chain troubles) and trends such as cryptocurrency are altering the financial world.
Tech can help slow climate change effects through conservation controls in homes, offices, cities, and power plants, even if “crypto-mining” has become an energy vampire. Likewise, as technology displaces many people in the workforce, it will create more new jobs than it destroys. The trick is ensuring that people are trained to do the work and opportunities don’t bypass women and minorities.
There are some threats to U.S. tech sectors, but also opportunities for Wisconsin to grow as a tech-savvy state.
In Washington, D.C., Congress should establish data privacy rules that are national in scope versus a state-by-state approach that could hamper companies engaged in eCommerce, finance, or insurance. Congress should avoid unnecessary taxes on venture capital managers and not pass an antitrust bill that would shut down “exit” options for young companies.
Congressional consensus around bipartisan plans to invest federal dollars in key research areas could help Wisconsin, especially if the state’s research universities and private partners can compete for one or more R&D “hubs” envisioned through the National Science Foundation.
In the Wisconsin Legislature, the refining of the state’s investor tax-credit law will lead to more angel and venture capital dollars flowing into young companies. When the Qualified New Business Venture law took effect in 2005, angel and venture capital investments could be measured in the tens of millions of dollars. The 2021 total will easily exceed $500 million, in part because those credits are pulling four times their weight in private investment. Pending bills would improve the law.
The new year may be tumultuous in many ways, but growth in tech markets could help smooth choppy waters.
—
The Wisconsin Technology Council is the independent, non-partisan science and technology advisor to the governor and the Legislature.
FIPCO partners with interface.ai
In this current world, customer connection comes at a premium. The pandemic changed many things and shifted customer behavior. Now customers who may have previously stopped by a branch to ask a question are seeking service through phone more and more. How can financial institutions manage the ever-increasing number of calls while still providing high-quality service?
FIPCO is proud to announce a new partnership with interface.ai. interface.ai’s artificial intelligence (AI)-Powered Phone Banking solves many of the problems faced by traditional call center, elevating the entire call center experience. The AI-Powered Phone Banking automates more than 60% of the financial institution’s call center calls using the industry’s first neural voice-powered AI assistant.
“We are thrilled to be able to partner with interface.ai to offer this world-class product to our customers,” said Pam Kelly, president of FIPCO. “We understand the need for effective service for everyone who calls an institution, while making sure call center staff are not overwhelmed and customers aren’t stuck waiting for help in a queue.”
The AI-Powered Phone Banking reduces call wait times, while increasing productivity and engagement. FIPCO and interface.ai will be hosting informational webinars on November 9 and 16 to demonstrate to capabilities of this solution.
To learn more about this solution and the upcoming demos, contact FIPCO Sales at fipcosales@fipco.com or 1-800-722-3498, option 5.
Upcoming Informational Webinars:
Date: November 9, 2021
Time: 12:30 PM – 1:30 PM CTDate: November 16, 2021
Time: 11:30 AM – 12:30 PM CT
By Cassandra Krause
With a recent uptick in activity, ransomware attacks are a form of cyberattack that has been prevalent in recent news — and for good reason. The effects can be detrimental in terms of monetary loss and reputational damage to the victim. Ransomware is a type of malicious software (a.k.a. malware) that usually encrypts a victim’s files, and the bad actors have upped their game to steal the data first, then threaten to also publish the data to the public. Criminals set their sights on businesses with the goal of extorting money, making community banks prime targets.
Organized crime networks are becoming increasingly sophisticated. In general, the risk of getting caught for cybercrimes is much lower than for traditional crimes like robbery, and the financial gains are far higher. Ransomware developers write and sell the software to other bad actors for a cut of the profits when they deploy it and collect ransom payment, usually in the form of cryptocurrency, which is hard to trace. Compromised data may also be used to open fraudulent lines of credit.
“The U.S. is in a ransomware crisis right now,” said Jeff Otteson, vice president of sales at Midwest Bankers Insurance Services (MBIS), a subsidiary of the Wisconsin Bankers Association. He explained that it has created a hard insurance market with carriers tightening up on internal control requirements such as multifactor authentication (MFA) for privileged users (users with the ability to install software or change security settings on critical systems) and encryption of backups.
In their 2021 Cost of a Data Breach Report, IBM Security and the Ponemon Institute calculate that the average total cost of a data breach is $4.24 million, a 10% increase from 2020–2021. The per-record cost of personally identifiable information averaged $180.
Prevention
With the incredibly high stakes in mind, banks are dedicating significant resources to preventing malicious cyberactivity, both in terms of staff and money. Respondents to a 2020 Deloitte survey of financial institutions reported spending about 10.9% of their IT budget on cybersecurity on average, up from 10.1% in 2019. In terms of spending per employee, respondents spent about $2,700 on average per full-time employee (FTE) on cybersecurity in 2020, up from about $2,300 the prior year.
“There is an industry-standard framework for ransomware prevention and all cybersecurity,” explained FIPCO’s Director InfoSec and Audit Ken Shaurette. FIPCO is also a WBA subsidiary. A good consultant will walk the bank through a comprehensive review of their network security, improving endpoint protection to replace traditional antivirus and endpoint detection solutions, including adding authentication improvements such as MFA, improved password strength, and protecting backups. As more and more of the digital tools that bankers utilize require users to download and install software and updates, depending on signature-based solutions for malware detection is not acceptable — it has become critical to safeguard user, file, network, and device-level activities.
A bad actor gaining access to a bank’s data may encrypt the data and demand payment in exchange for granting access back to the bank. In this situation, having a data backup is essential.
“The rule of thumb for data backups is 3-2-1,” said FIPCO Information Security and IT Audit Advisor Rob Foxx. “There should be three copies of all data stored on two different mediums. One of the copies should be stored off site.”
Ransomware prevention is only one part of a complete cybersecurity system. Experts agree that early detection of unusual activity within a system can help keep a minor incident from quickly escalating into a major incident like a ransomware threat.
“Ransomware isn’t the first attack,” said Wolf & Company, P.C. Manager of the I.T. Assurance Group Sean Goodwin, who recently presented at WBA’s Secur-I.T. Conference. “Ultimately, it’s on I.T. to put controls in place because an employee will inevitably fall for a phishing email. It becomes a question of whether we can catch that quickly.”
Social engineering remains the greatest concern; it’s easier for bad actors to trick an employee rather than break through a firewall. Verizon’s 2021 Data Breach Investigations Report found that almost half of the breaches in the financial services industry involved internal actors committing various types of errors. The report stated that the financial sector frequently faces credential and ransomware attacks from external actors, 96% of which are financially motivated (followed by small percentages of motives of espionage, grudge, fun, and ideology).
Goodwin emphasized that I.T. must be able to act quickly when there’s an indication that someone is accessing something they don’t normally access. “Prevention is ideal. If we can prevent it, that’s best-case scenario, but if not, early detection becomes critical,” he said. This area of solution, known as endpoint detection and response, is rapidly becoming a key point of protection from ransomware and all other malicious events.
Establishing an incident response program within a bank is an important part of the overall cybersecurity program.
Preparation
Creating a culture of cybersecurity awareness throughout the bank is important, so that bank employees are prepared for an incident. Employee training on what to do in the event of an attack should be standard practice. Making security part of the organization’s DNA is a best practice.
“Every bank needs an incident response plan, and that needs to be approved all the way up through the board. Part of this plan is notification of incidents to the insurance carrier,” said MBIS’s Otteson.
FIPCO’s Foxx emphasized that the roles and responsibilities in the incident response plan must be clearly defined, and banks should revisit their plan regularly.
“As the insurance agent, I’m the first call a bank makes when there’s an incident,” said Otteson. “It’s important that banks choose to work with an agency that understands cyber insurance.”
MBIS insures about 220 banks and has access to a large number of carriers that provide the right coverage for their customers. Otteson recommends reporting all incidents as even a minor incident could result in a claim down the line and having reported that incident when it occurred is key to a successful claim. He says to keep in mind that the owner of the data is liable for it whether the incident occurred in house or with a vendor the bank shared customer data with.
Mitigation
It’s important to work with the insurance carrier to ensure that all the bases are covered and that the vendors who participate in the response are approved. Not using the cyber insurance carrier’s approved vendors may result in expenses not being covered under the insurance policy. In the event of a ransomware attack, the insurance agent or bank will immediately notify the insurance carrier. Beazley, a carrier partner of MBIS, maintains a 24/7 helpline, which has become common with other carriers as well. Knowing how to report incidents, when to report, and what to expect is key.
Holidays and weekends are prime times for ransomware attacks: employees who are in a rush to leave may be more likely to click on a bad link, and with employees away from work, it’s easier for the bad actors to get into the network. Even if a problem is detected, it’s more likely that staff who could help put a stop to the attack may be on vacation or unavailable, buying the criminals more time to take over.
As soon as a cyber liability claim is made, the insurance carrier’s pre-approved vendors come into play.
“Nobody has the resources in house to effectively manage ransomware attacks,” said Foxx, who has experience working both within a bank and as an external auditor and consultant. The specialization of skills and the amount of people needed to perform adequate analysis and remediation are so significant that even large banks will not have all the players they need on staff.
If a bank’s data becomes encrypted and made inaccessible, a vendor such as Tetra Defense would be engaged on forensics. Managed endpoint detection and response vendors such as Cynet can help from detection and prevention to response, including providing digital evidence for a vendor performing forensics. Meanwhile, a vendor such as Coveware would handle ransom negotiations with the criminals. Wolf & Company, P.C.’s Goodwin said that you don’t really know who’s on the other side of the transaction — some criminals may be willing to negotiate and others not. He referred to ransomware as a “niche space in cybersecurity that is now getting more attention.” The criminal organizations involved in these types of attacks in some ways act like a legitimate business in that they rely on their reputation and may even have customer service departments — if they fail, it will hurt their chances of getting more business in the future.
Typically, in the event of a ransomware attack, a legal firm will handle communications and PR for the bank — putting a statement on the bank’s website, assisting staff with customer phone calls, and determining whom to notify. Getting legal involved early protects all communications and discovery with attorney-client privilege. The requirements for notification vary from state to state, and a bank may have customers in multiple states or even other countries, making the expertise of a legal team invaluable. The language used in communications matters, as the term “breach,” for example, can have different legal implications and potentially create larger issues than terms like “incident,” “situation,” or “event.” Education of staff far in advance using regular testing of the plan is a key factor in mitigating an incident. Inappropriate statements made by employees on social media or even at informal social gatherings can have severe ramifications for the bank.
Follow Up
While anyone who experiences a ransomware attack may be eager to breathe a sigh of relief and move on when it is over, it is essential to review the incident and revise the bank’s incidence response plan. Assessing what went well and what needs to be improved are critical steps.
Goodwin also warns that victims of ransomware are commonly re-targeted. A Cybereason study found that 80% of organizations that previously paid ransom demands confirmed they were exposed to a second attack. He said that once a company has paid a ransom it is known that (1) you were compromised, (2) you do not have proper backups of your files, and (3) you were willing to pay.
Summary
Cyberattacks are the biggest risk to a financial institution — even surpassing the risk of past-due loans. The cost of a ransomware attack can be astronomical, with many factors contributing to the price tag, including vendor fees and staff hours to resolve the issue; the cost to inform customers and offer identity or other protections; the loss of destructed data; and the down time of the business. All of this, followed by the loss of customers’ trust (and subsequent loss of their business), has the potential to put a community bank out of business.
There are safeguards banks can put in place, including a sound incident response plan, improved monitoring with better endpoint detection and response, cyber liability coverage, and employee education. FIPCO, MBIS, and a wide range of WBA Associate Members are ready to support banks in keeping their data and that of their customers safe.
Five critical steps to maintaining a secure network.
Keeping your network secure in the current climate of internet assault is no small job.
Think back – how little has changed. In 2001, server-based worms were estimated to have cost private industry almost $3 billion. Code Red alone infected 359,000 servers in under 14 hours, and within 24 hours of Nimda, 50 percent of the infected hosts went offline. Fast forward to today and the exponential increase in breaches, how much is really that different?
These attacks reinforced the need for every organization to develop an information security action plan (ISAP). Doing this first involves evaluating, assessing, and auditing the existing security environment to identify major and minor problems (your inventory). Without knowing and understanding the current security posture, it is impossible to identify the most cost-effective solutions to deploy.
Veteran and well-trained security professionals realize there is no ‘silver bullet’ in information security. Following and adjusting to an industry security framework will keep you secure today and into the future. Using proper diligence to understand an organization’s security needs goes a long way in improving protection.
The following are critical first steps for building an ISAP to create a better defense in an increasingly dangerous cyberworld.
Creating Security Policy
First, create a clearly defined security policy that is strictly enforced. Understand that security goes beyond desktop PCs and ensure that the use of all laptops, copiers, fax machines, modems, and even printed information is included in the policy. Supply the policy to everyone in the organization, educate all employees about it, and enforce it consistently.
The policy is the roadmap to good security, and every employee should review it annually, be provided with opportunities to ask questions, and fully understand the policy. They should acknowledge their understanding of the policy in writing. The policy must become a standard part of the company culture and be enforced at the highest level. Not consistently enforcing policy can be worse than having no policy at all, because it could be used against the company (in litigation) to show that policy is not taken seriously in all cases.
Identifying Risk, Deploying Security
Second, identify an acceptable level of risk and deploy the appropriate level of security. It is no longer adequate for management to proclaim ignorance about potential vulnerabilities in the environment. Due diligence requires management to exercise sound judgment in protecting the environment consistent with the information being processed (i.e., the more sensitive the information, the more safeguards need to put in place).
After assessments have been performed, there are essentially three measures that can be taken. They are to reduce the risk (perform remediation), transfer the risk (take out insurance), or accept the risk (identify cost justification).
If overall risk reaches an unacceptable level, appropriate remediation steps must be taken to get the exposures reduced in severity. If that cannot be done, documentation must be created to identify justification for accepting the risk, or possibly insurance can be purchased to transfer the losses associated with the risk to another organization.
Implementing Verification
Third, access to internal hosts must be controlled and monitored. Are employees only given access to what they need to perform their specific job? Are logs reviewed daily for inconsistencies and abnormalities?
Since many security breaches can be attributed to ‘insiders,’ or exploit by a bad actor of an insider, trust no one. “Zero Trust”; it is important to live by an access philosophy of ‘least privilege’. Verify everyone and everything. Only give users the access they need to do their job. Not only must the data be protected and accountability of who is accessing it be maintained to ensure privacy, but simply tracking problems and events that occur in an environment are easier if it is possible to determine who has access to specific information. Even though incidents of access from outside a company get all the publicity, the most critical protection remains inside. Insider abuse of email or unmonitored internet access can cost in several ways beyond the lost employee time, bandwidth, and potential for viruses or worms.
Supplement the authentication and authorization system with audit trails and intrusion detection systems and use an incident response plan to follow up on suspicious activities and anomalies. Logs can be very large and contain enormous amounts of extraneous information. It is important to install tools that help sift through the abnormalities or make it possible to identify what a normal log looks like and flag unusual activity. Regular review of system logs can mitigate risk. This can include the implementation of modern extended endpoint detection and response solutions.
Testing Upgrades and Patches
Fourth, vendor upgrades and software/hardware patches should be tested adequately before migrating to production. Anti-virus tools should be deployed and automatically updated with new signature files.
Changes are constantly occurring in the environment. New software can introduce new vulnerabilities and it is well-known that some software companies do not create secure applications or operating systems. Be sure to have clear documentation to migrate all changes to production and a contingency plan should problems occur.
Malicious code continues to be a major problem for organizations. It is no longer adequate to simply install an antivirus tool and assume your problems are alleviated. It is not adequate to assume the user will behave properly to protect their desktop and company data. Today’s generation of protection must not be dependent on signatures and needs to consider other layers of information: users, files, hosts, and the network. Throw in deception technology and you have a robust solution.
Handling Any Defaults
Fifth, be sure default accounts, passwords, and settings have been appropriately handled in operating systems, routers, databases, and applications.
Keep in mind that almost all operating systems, including third-party applications, come with sample files, many of which are extremely dangerous. Almost any operating system and many application system installations require a powerful ‘administrative’ or privileged account to complete installation. This account is shipped with a default password, which often is not changed by the network, system, or application administrator. It should be changed immediately at initial installation even on test systems. If the account needs to remain in existence, it should be tightly locked down, audited, and, if possible, have its default name changed. In addition, it should not be used on a routine basis for administration. Individual administrative accounts should be assigned to authorized users with proper access requirements granted, training provided, and responsibilities understood.
In summary, there are numerous measures that can be taken to ensure a company’s infrastructure can protect its information assets. This all creates the requirement for a thorough information security action plan. A certified, qualified, well-trained chief information security officer can usually lead a corporation along a path to protected information assets and a secure business environment.
To learn more, call or email Ken Shaurette, FIPCO's Director – Information Security and Audit, at 800-722-3498 ext. 251 or itservices@fipco.com today.
By, Ally Bates
Resurgence of rare charter may reshape the banking industry
The FDIC has two decisions to make that will have a tremendous impact on the financial services industry. On June 6, online personal finance company Social Finance, Inc.* (better known as "SoFi") applied for an industrial loan charter (ILC) for the purposes of offering FDIC-insured NOW deposit accounts and credit card products—this in addition to the student loan refinancing, mortgages, and personal loans the company already offers its customers. The de novo would be chartered in Utah under the name SoFi Bank. On September 7, payments giant Square filed its application** for a Utah-based ILC for the purposes of expanding its lending arm—in addition to payments, Square also offers small business and consumer loans. While (at the time of this writing) the FDIC has yet to take action, approval or denial of these applications will set the stage for the next phase of bank-fintech relations.
Historical Context
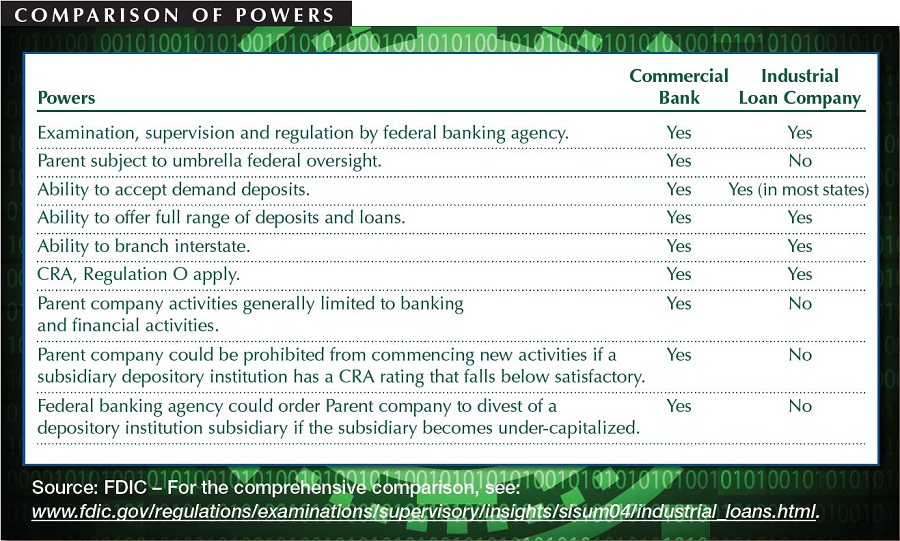
Now state-chartered companies operating with federal deposit insurance, the ILC business model has been in existence since the early 1900s. Since their inception, non-bank retail companies have used these entities primarily to make consumer finance loans in order to sell their products, explained Attorney James Sheriff, partner at Reinhart Boerner Van Deuren, s.c. For example, BMW, General Motors, and Target all had industrial bank subsidiaries (and some still do). "The charter allows commercial companies to own financial institutions that can take federally insured deposits," explained Attorney Patrick Neuman, partner at Boardman and Clark, LLP. This bucks the long-standing policy in the U.S. to separate commerce and banking, a policy created in 1933 by the Glass-Steagall Act and reinforced by the Bank Holding Company Act of 1956 (BHCA).
Only seven states currently have provisions allowing for ILCs: California, Colorado, Minnesota, Indiana, Hawaii, Nevada, and Utah (where the vast majority of industrial banks are headquartered). Due to their exemption from the BHCA, ILCs are regulated only by their chartering state regulator (the Utah Department of Financial Institutions oversees ILCs with over $143 billion in combined assets) and the FDIC. The Federal Reserve has no authority to regulate the activities of the parent company, which—unlike traditional charters—is not limited to activities that are substantially related to banking.
However attractive this charter may seem, it has not been a popular option in recent years. No ILC applications were filed between 2009 and SoFi's application in June 2017—a timeframe which includes a three-year moratorium imposed by the Dodd-Frank Act (lifted in 2013). The last company to garner attention for its ILC application was Walmart in the mid-2000s. Fearing the retail juggernaut's entry into retail banking, the banking industry successfully lobbied for laws in several states (including Wisconsin) prohibiting ILCs from having a banking facility within 1.5 miles of a retail location owned by the same parent company. At the time, it was considered a great success. However, today's applicants aren't interested in physical retail locations. "Before, the goal was to bring consumers into the store in order to win their banking business," Sheriff explained. "Today, the brick-and-mortar isn't important, but rather wanting to expand financial products and services. It's a different threat."
Renewed Appeal
The current financial services landscape is ripe for renewed interest in ILCs. Technological advances have made brick-and-mortar branches unnecessary and nation-wide reach attainable. However, banking's regulatory structure has not kept pace with the change. "Right now, in order to be a financer these companies need to get licensed in all states they do business in," Sheriff explained. One of the biggest attractions of an ILC is the federal pre-emption it offers. "Instead of 50 state regulators examining your consumer finance company, there's one state and the FDIC," he said.
Another major draw of an ILC is that it allows the parent company to retain the flexibility to experiment that fintech startups are known for. "SoFi is a tech company and doesn't want to be hamstrung by the Bank Holding Company Act," said Neuman. "ILCs are not subject to consolidated supervision at the holding company level. That's a big advantage."
Operationally, fintech companies like SoFi and Square would receive another important benefit from obtaining an ILC: a stable funding source. "Both companies make loans, and if they get an industrial loan charter they get access to federally insured deposits. Deposits are a significantly less expensive source of funding than investment capital or bonds," Neuman explained. The availability of government-backed deposits as a funding source would alleviate concerns over whether institutional funding is stable enough to weather an economic downturn or significant market fluctuation.
What Happens If…
FDIC's approval of either pending ILC application would have profound implications for the future of the financial services industry. "If the FDIC decides to approve one of those applications, it could be a game-changer," said Neuman. "If either application is approved, there will be a flood of new applications." If SoFi or Square does receive an ILC, the banking industry will need to prepare for several long-term effects.
First is a new, aggressive source of competition. "The most often-cited concern with ILCs is that they could lead to a concentration of economic power in banking," said Neuman. With ILC charters, giant technology retail companies like Apple, Amazon, and Google could offer the same products to consumers as banks. "They'd be behemoths to deal with in a consumer or small business banking sector," said Sheriff. In addition, those companies' data collection activities would not be restricted by the BHCA, enabling them to obtain and analyze consumer data that is not available to most banks. "That could seriously undermine a bank's ability to compete," said Neuman. One area where the competition could be especially fierce is in small business lending. "If the ILC option becomes more popular, and if small fintech lenders like Prosper get these charters, it would create a lot more competition for community banks in small business lending," said Sheriff. "It has some real potential detriments for community banks."
Another concern directly relates to SoFi's business model, which is driven by a focus on HENRY customers (High Earner Not Rich Yet). "Much of their business is student loan financing for professionals such as doctors and lawyers. There's concern in the industry that fintech lenders won't adequately serve the working class household or be able to meet CRA requirements," Neuman explained. "This type of business model could lead to a disproportionate allocation of credit." Banks can only speculate how the state regulators and FDIC will address CRA concerns with ILCs.
Increased popularity of ILCs may also dampen partnerships between banks and fintech companies—partnerships that currently expand product and service offerings for many bank customers. "If FDIC starts approving these charters, there will be fewer partnerships between fintechs and banks," said Sheriff. "The fintech companies will no longer need to partner in order to get data and deposits." This is not conjecture. Former SoFi CEO Michael Cagney told TechCrunch the company plans to offer checking, deposit, and credit card services through a regional banking partner if the ILC application is not approved.
Finally, ILC opponents see increased risk to the industry as a whole if these charters have a resurgence among technology companies. "What happens if one of these goes through and becomes huge, but then the parent company makes some wild bet and goes under? That could be a huge hit to the FDIC and the banking industry in general," Sheriff said. "Bank regulators aren't familiar with how to evaluate some of those widespread risks. We've separated banking and commerce for 85 years for a reason." The same concern applies to the potential for further increasing the market power of the "Big Five" (Amazon, Apple, Facebook, Google, and Microsoft) by adding banking services to their already diverse lines of business.
What if the FDIC denies the pending applications? Will community banks be able to breathe a sigh of relief and go back to business-as-usual? Probably not. "If these fintech companies don't get approval for an ILC, I believe they'll pursue other avenues, such as an OCC fintech charter," said Neuman. "Banks are going to see fintech as a real competitor in the lending space, and sooner rather than later." Influencer companies in the technology sector have set their sights on banking products, and they won't be easily deterred. "The bottom line is that there is activity in this area right now," said Sheriff. "This isn't hypothetical."
Boardman and Clark, LLP is a WBA Gold Associate Member.
Reinhart Boerner Van Deuren, s.c. is a WBA Associate Member.
*View a copy of SoFi's application here. On October 13, SoFi withdrew its application for an ILC charter as it undergoes a leadership transistion, but says "a bank charter remains an attractive option."
**Square's ILC will be named Square Financial Services, Inc., according to a Wall Street Journal report.
By, Amber Seitz
Three Wisconsin institutions prove you don't need to be big to benefit from technology
The banking industry is undergoing a period of massive change in many areas (technology, compliance, competition, etc.), but one of the most significant has been in progress for over a decade. Over the past ten to fifteen years, banks have been gradually replacing in-person, customer-facing operations with technology—account opening and loan applications, for example. The concept of using technology to augment human relationships is relatively new to banking, but Wisconsin Banker interviewed three Wisconsin banks who have done so successfully, each in a unique way.
Customer Convenience – Digital Channels
Waterloo-based Farmers & Merchants State Bank has offered online mortgage applications since May 2008 and added a mobile banking app five years ago, and they've seen results. "In the last five years we've gone from $95 million to $153 million in loans serviced for the secondary market, largely due to the online applications," said Executive Vice President & CFO William Hogan, CPA. After an initial lag in adoption rates, Chief Marketing Officer and Bank Manager Kim Abraham says marketing helped the online applications grow in popularity, but customers are also becoming more accustomed to doing things online. "Their comfort level with technology changed," she explained. Hogan notes that the product also markets itself through referrals, since customers who love the convenience of being able to start their application anytime often recommend it to others.
Internally, the bank decided to implement the online mortgage application product (which includes HELOCs) as a tactic to build their secondary market servicing portfolio. However, it also enhanced the perception of the bank and their products and services in the community. "We recognized that this was a way for us to not only be seen as a small town community bank with big banks products and competitive rates, but also as viable option and player in the surrounding communities and Madison market," said Abraham.
The bank's mobile app has also been impactful, partly due to steady increase in users of the mobile deposit feature. "We were one of the early adopters of mobile deposit capture," Hogan said (the bank launched the product in June 2013). "There's been a steady adoption of that." One of the reasons usage of the bank's app continues to grow is the periodic additions of new features, such as mobile bill pay. "We're constantly looking at the mobile app and adding to it," Hogan explained. He knew the bank needed to invest in mobile the day he walked around the office and saw everyone with a smartphone. "It's just the way to go," he said. The bank's goal with each of these tools was to make connecting with customers easier. "Customer convenience is one of the primary drivers behind our technology," said Abraham.
Speedy Service – Compliance Concierge
Mayville Savings Bank was one of the first institutions to use FIPCO's Compliance Concierge loan origination and deposit account opening software suite when it launched in 2012, but they've been using software for lending for many years. "We are trying to follow technology as fast as it's moving," said Loan Processor LaRue Wills, who also sits on the FIPCO Users Committee. "Our small little community bank wants to be able to offer what larger regionals are offering their customers." Being fast adopters of software has increased speed-of-service for the bank's customers and internal efficiencies, as well as allowing the bank to offer mortgage products it previously could not.
One of Wills' favorite features of Compliance Concierge is an upgrade the bank purchased: a credit reporting interface with Factual Data. "It makes it so nice to be able to take an application, do a credit report and have all the information fill in automatically," she said. The software also allows bank staff to offer faster service. "The time-saving for customers is excellent," Wills said. "Customers can walk into the bank and get taken care of in an hour." Leveraging the software to its full capacity has also helped the bank operate more efficiently, according to Wills. "If a customer wants to get a loan and switch their deposit account to us, it's much easier now for all of that to go into one system," she explained. "Banks that only have the deposit side or only the loan side don't know what they're missing."
The bank's decision to invest in technology like online banking and Compliance Concierge has also enabled it to offer fixed-rate mortgage loans, a product they previously were not able to offer their customers. "We are a small community bank with only one branch, we're as small as they come," said Wills. "Now we're able to offer our customers fixed-rate loans and that's due to the convenience of having Compliance Concierge be able to upload the required information for selling them on the secondary market directly to the bank we use. Before, we couldn't help a customer who would only do a fixed-rate loan. Now we can serve them."
Full-Service Machines – QwikBank ATMs
Two years ago, Superior Savings Bank decided to consolidate some of its branch locations to improve efficiencies—branch transactions had been steadily declining due to the popularity of the bank's electronic services. "Management and the board felt the need to replace two of the bank's high-cost branch offices with a solution that would provide customers with similar convenience," President Dawn Staples explained. Four months after closing a branch in the Walmart Supercenter on the west side of Superior, the bank installed its first QwikBank ATM just across the parking lot. Shortly after that, a second QwikBank ATM was installed on the east side of Superior. "The main goal was to mirror the services provided when the bank had three staffed locations in Superior," Staples said. "In addition to making cost-free ATM access available to its debit card customers, the bank wished to provide the ability for them to deposit cash and checks at locations in addition to the main office in the downtown."
The QwikBank ATMs have several features, including typical ATM functions like cash withdrawal and checking balances, but one of the most popular is a transaction previously only available in the teller line. "Our favorite feature of these full-service ATMs is the customers' ability to deposit cash and checks into their accounts with immediate availability," said Staples. "This essentially enables the bank's customers to cash a check at the ATM." To promote this new way for customers to interact with the bank, the main office tellers have undertaken a continuous customer education process, which Staples says has been successful. "The reaction of the bank's customers has been very positive," she said. "The key is getting the word out about the QwikBank locations and capabilities."
Ultimately, the QwikBank ATMs are just one more tool in the bank's technology repertoire. "For a small bank, Superior Savings Bank has capably matched its larger competitors in providing electronic banking solutions," said Staples. "In addition to the full-service ATMs, we offer internet banking, bill pay, mobile banking and remote deposit capture." That comprehensive approach to technology has helped the bank set itself apart in the communities it serves.
FIPCO is a wholly owned WBA subsidiary.
By, Amber Seitz